Risk Management Enterprise - Truths
Wiki Article
The 8-Second Trick For Risk Management Enterprise
Table of ContentsUnknown Facts About Risk Management EnterpriseWhat Does Risk Management Enterprise Mean?Risk Management Enterprise Can Be Fun For AnyoneRisk Management Enterprise - TruthsThe Buzz on Risk Management Enterprise4 Simple Techniques For Risk Management EnterpriseThe Only Guide for Risk Management Enterprise
Below are several of its key attributes that facilities must understand. Take a look. Real-Time Threat Assessments and Reduction in this software program enable companies to continually check and evaluate risks as they progress. This attribute leverages real-time data and automatic analysis to determine possible risks promptly. Once threats are determined, the software application promotes prompt mitigation actions.
KRIs resolve the issue of inconsistent or vague threat analysis. They attend to the difficulty of continuous threat administration by offering tools to check risks continuously. KRIs boost protection danger oversight, ensuring that prospective dangers are identified and taken care of effectively. The job of danger management ought to not be a difficulty. Companies have to count on an excellent and sophisticated threat monitoring software program.
Unknown Facts About Risk Management Enterprise
IT take the chance of management is a part of venture danger management (ERM), developed to bring IT take the chance of according to an organization's risk hunger. IT take the chance of administration (ITRM) includes the plans, treatments and modern technology needed to minimize threats and vulnerabilities, while maintaining conformity with relevant regulatory needs. Furthermore, ITRM looks for to limit the effects of destructive occasions, such as safety breaches.Veronica Rose, ISACA board director and an information systems auditor at Metropol Corp. The ISACA Risk IT framework lines up well with the COBIT 2019 structure, Rose claimed.
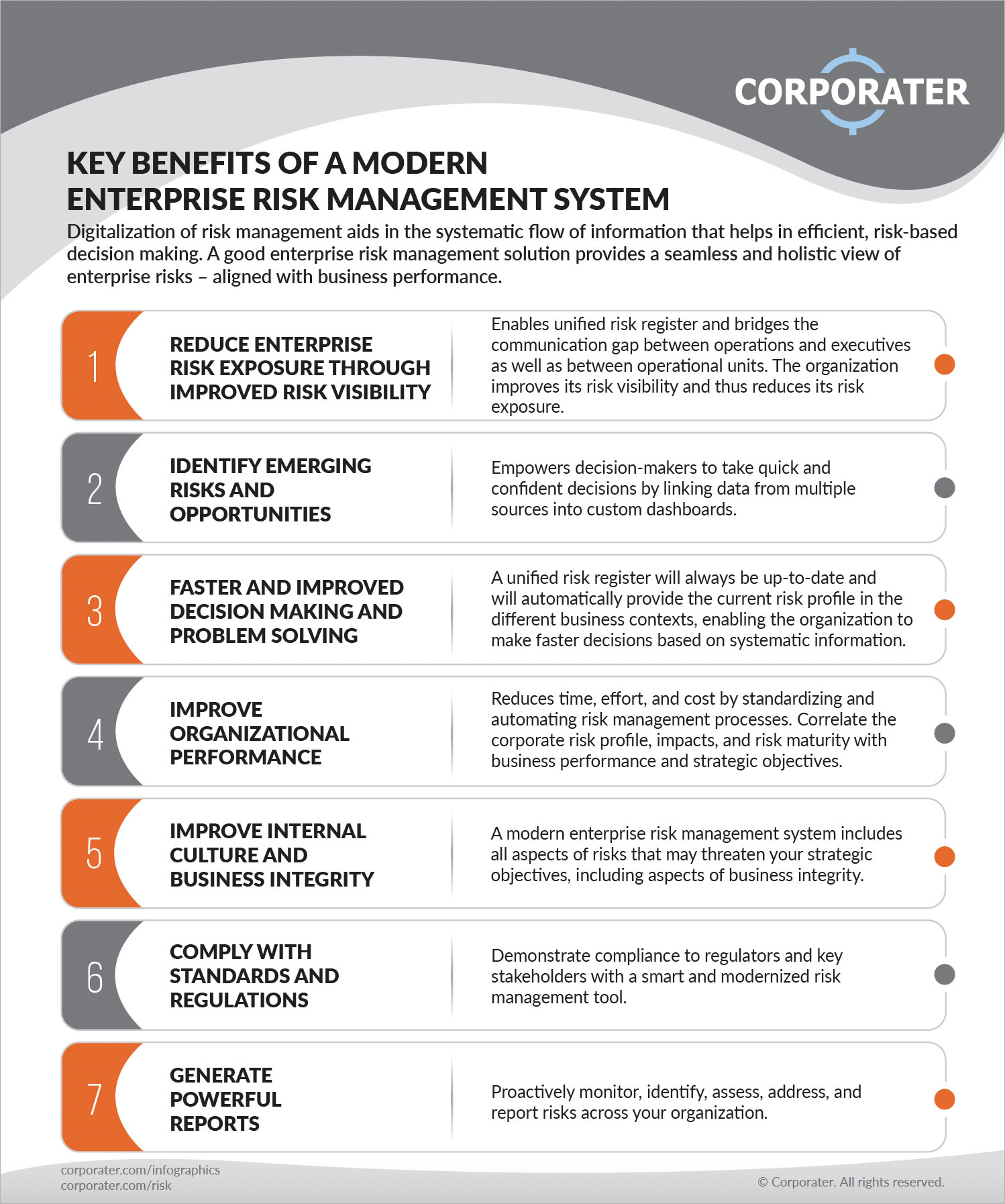
Venture Threat Monitoring Software Growth: Benefits & Features, Expense. With technological advancements, risks are continually increasing. That being claimed, companies are most likely to encounter difficulties that influence their financial resources, operations, and online reputation. From rapidly fluctuating markets to governing changes and cyber risks, services browse via a constantly transforming sea of risks.
Some Ideas on Risk Management Enterprise You Need To Know
In this blog, we will certainly study the globe of ERM software program, exploring what it is, its advantages, attributes, and so on to ensure that you can construct one for your company. Business Threat Administration (ERM) software application is the application program for planning, directing, organizing, and managing business activities and simplifying danger management processes.With ERM, organizations can make informative decisions to boost the general strength of business. Read: ERP Application Growth Devoted ERM systems are critical for organizations that routinely handle large amounts of delicate info and numerous stakeholders to authorize strategic choices. Some sectors where ERM has actually become a conventional system are medical care, money, construction, insurance coverage, and infotech (IT).
: It is demanding for any kind of enterprise to undertake a comprehensive audit. It can be avoided by making use of the ERM software system. This system automates policy compliance administration to keep the company protected and compliant. Besides that, it also logs and classifies all the data in the system making it much easier for auditors to examine processes a lot faster.
The smart Trick of Risk Management Enterprise That Nobody is Discussing
You can additionally attach existing software program systems to the ERM via APIs or by adding data manually. Services can utilize ERM to review dangers based on their prospective effect for better risk administration and mitigation.: Including this attribute permits users to get real-time notifications on their gadgets concerning any type Find Out More of risk that could occur and its impact.
Rather, the software permits them to establish thresholds for various procedures and send out push alerts in case of feasible threats.: By incorporating data visualization and reporting in the personalized ERM software, businesses can gain clear understandings regarding danger trends and performance.: It is compulsory for companies to adhere to market conformity and regulative standards.

These systems enable companies to implement best-practice danger administration processes that straighten with industry requirements, using a powerful, technology-driven technique to identifying, evaluating, and mitigating dangers. This blog checks out the benefits of computerized threat monitoring tools, the areas of threat administration they can automate, and the value they offer an organization.
8 Easy Facts About Risk Management Enterprise Explained
Groups can establish kinds with the relevant fields and easily create different forms for different risk types. These threat analysis kinds can be flowed for conclusion using automated operations that send out notices to the appropriate personnel to complete the forms online. If forms are not completed by the target date, after that chaser e-mails are immediately sent by the system.The control monitoring and control testing procedure can additionally be automated. Companies can make use of automatic process to send out normal control examination notices and staff can get in the outcomes by means of on the internet forms. Controls can additionally be monitored by the software program by establishing regulations to send informs based upon control data kept in various other systems and spread sheets that is pulled right into the system using API integrations.
Risk administration automation software program can additionally support with threat reporting for all degrees of the venture. Leaders can check out records on threat exposure and control efficiency via a range of reporting results including fixed records, Power BI interactive reports, bowtie evaluation, and Monte Carlo simulations. The capability to pull genuine time reports at the touch of a switch reduces out difficult data adjustment tasks leaving threat teams with even more time to assess the investigate this site data and suggest the service on the very best strategy.
The need for efficient has never ever been more important. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can't pay for hold-ups or ineffectiveness in addressing prospective threats. Standard threat management utilizing hand-operated spreadsheet-based processes, while acquainted, typically result in fragmented information, time-consuming reporting, and a boosted chance of human error. Automating the risk administration procedure with software application addresses these imperfections.
The Single Strategy To Use For Risk Management Enterprise
This ensures threat signs up are constantly present and straightened with business goals. Compliance is another critical driver for automating risk monitoring. Requirements like ISO 31000, CPS 230 and COSO all supply assistance around threat administration best techniques and control frameworks, and automated threat administration tools are structured to line up with these requirements aiding companies to satisfy most commonly utilized threat management requirements.Search for threat software systems with a consents power structure to easily establish up process for risk acceleration. This capability enables you to customize the view for every customer, so they only see the information relevant to them. Make certain the ERM software program provides individual tracking so you can see that entered what information and when.
Choose a cloud-based system to guarantee the system gets routine updates from the supplier adding new functionality. Choose tools that provide job danger management abilities to manage your projects and portfolios and the linked threats. The advantages of taking on danger monitoring automation software expand far beyond efficiency. Organizations that incorporate these remedies right into their ERM approach can anticipate a host of concrete and intangible.
Excitement About Risk Management Enterprise
While the case for automation is engaging, executing a risk monitoring platform is not without its obstacles. For one, information high quality is crucial. Automated systems count on exact, updated information to provide meaningful insights. To overcome the difficulties of risk administration automation, companies should purchase data cleaning and governance to make certain a strong foundation for executing an automated system.Automation in danger management equips services to change their method to risk and construct a more powerful foundation for the future (Risk Management Enterprise). The concern is no much longer whether to automate danger monitoring, it's just how soon you can start. To see the Riskonnect blog in action,
The solution often lies in exactly how well risks are expected and managed. Job management software program offers as the navigator in the turbulent waters of task execution, offering devices that identify and examine threats and create strategies to mitigate them properly.
Report this wiki page